The internet is continually evolving, and that means there are constantly new threats that people are going to use in an attempt to steal some of your data. Who knows what their reasons are, from "Because I can" to selling your information for money and many ideas that probably don't cross your (or my) mind. The important thing is to do everthing you can to make yourself safe. Here are some quick tips.
Learn the lingo: First some links to get you up to speed on the threats you're facing. Viruses, Phishing, Trojans, and Spyware are some of the most common attacks you will encounter. You don't need to read the entire page, but it's worth checking out the first paragraph and understanding the differences between a virus, trojan, and spyware.
Anti-Virus (Windows specific*): If you've bought a computer from a reseller, the liklihood that it came with a bunch of software pre-installed is high. You've probably got some software giving you a "free" evaluation and then nagging you to buy (and not protecting you in the interim). Forget all of that - uninstall that junk (while you're in there, scroll through the list and take a look at anything else that you no longer need and clean it out too). In this case, Microsoft is actually providing a very good free product called Microsoft Security Essentials. Download this and install it and never worry about getting nagged again. Avast! and AVG are other free alternatives, but lately they've been pushing their upgrades to their paid services a little too hard for my liking, and MSE has tested very well so I just don't see a reason to look at another product.
If you are uncomfortable with a free product, at least buy something that does a good job. BitDefender Total Security is a great product, but don't take my word for it. Visit www.av-comparatives.org for independent testing results of many popular AV packages.
*Just because I say this is Windows specific doesn't mean that Macs, Linux systems, or even your smartphones are safe from unwanted software. Always be careful about what you run on your computers/devices, and investigate protective measures for those systems. Google is your friend!
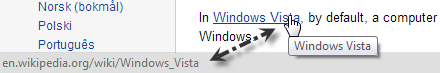
Learn what you're clicking: If you get a message from anyone that asks you to click here, you can do a very simple check to see where it's taking you. Hover your mouse over the link, and your browser will show where the link goes in the bottom left corner. This looks a little different depending which browser you're using, but they all do it. Look at that click here link in the opening sentence, would you go there?
Sometimes the link will be too long for the line that pops up in the bottom left of your browser - in this case, right click the link, select "Copy URL"/"Copy Link Address" or your browsers variant of that line, and then right click in your address bar at the top of your browser and select "Paste" (Do not choose "Paste and Go" or similar options - if you want to be super safe, paste into a Notepad or Word document). Voila, the entire link is revealed for you to look at.
Finally, be on the lookout for sneaky domain name tricks. If you receive an e-mail claiming to be from your bank, and it wants you to visit www.rbcroyalbank.com.banking.tw, this is not safe. You need to read domains from right to left, and if it doesn't end in .com followed immediately by the domain you expect, this is a scam. If you're not sure what the domain should look like, try getting there organically via your bookmarks or through a Google search.
Report spam: If you use a webmail service (GMail, Hotmail/Outlook.com, Yahoo, etc.) and receive a message in your inbox that is spam, a scam, or in some other fashion "not good", don't just delete it. Use your provider's "Report Spam" feature. Not only will this help similar messages that come to you in the future automatically go into the spam bucket, but it also helps the provider learn what kind of spam is defeating its filter so they can improve them.
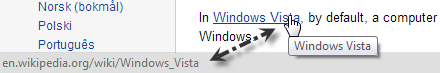
Watch for secure sites: Whenever you're doing anything online that involves money (banking, online shopping, etc.), take a look at your address bar and make sure you're on a secure connection. Most browsers will show you a lock icon that should be closed if everything is okay. If it's not, you can click on it to find out more.
 A secure connection in Chrome
A secure connection in Chrome
 A secure connection in Firefox (lock circled)
A secure connection in Firefox (lock circled)
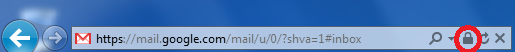 A secure connection in IE (lock circled)
A secure connection in IE (lock circled)
If you are on a site that is asking for credit card information and the connection isn't secure, stop! Perhaps their website made a mistake and you can just replace http:// with https:// at the front of the address bar and you will be secure. If that doesn't work, find another place to make your purchase. If you absolutely have to buy from that website, find a contact form and ask why their website isn't secure and if you can make the transaction another way, such as over the phone - don't send your credit card details by e-mail, this isn't secure either!
Two-factor authentication: Sometimes referred to as "two-step authentication", this means that you will have to login to a service with not only your password, but a second piece of information that verifies you are who you say you are. This type of system is often used to protect online banking and remote access to corporate data, but has become more popular in the e-mail space as it makes hacking your account nearly impossible. Typically this is in the form of a small application you can install on your smartphone, or alternatively via receiving SMS text messages on your mobile phone. If you use a Google-based mail service, check their documentation on setting up 2-step verification here. If you use a Yahoo! mail account, details on their system are here. Your Microsoft account (for outlook.com for instance) can be protected with two-factor authentication by following the steps here.
If you're not using a web-based e-mail account like one of the three listed above, you are less likely to be the victim of a phishing attack, but by no means are you immune. Choose a strong and unique password for your mail (see next section), and investigate whether two-factor authentication is available from your provider for that extra security.
Re-think passwords: Last but definitely not least, you need to re-think your passwords. Although brute-force hacking of passwords is still rare - this is where someone simply tries every combination of letters and numbers until they find your password - it is possible and as computers get faster it means they can test more combinations faster. An 8 character password, even with capitals and special characters, just isn't that strong any more. Combine this with the fact that we all usually choose one password and then use it everywhere, and it means that when your hobby website gets compromised and the vandals walk away with your password from there, they can then try to figure out where else you might visit and use that password to login there. The implication here is that you need a strong password whenever you are asked for one, and furthermore, it should be unique for every site you visit. I'm sure images of post-it notes or other horrifying thoughts are strolling through your imagination right now, but there is a simple answer to this problem.
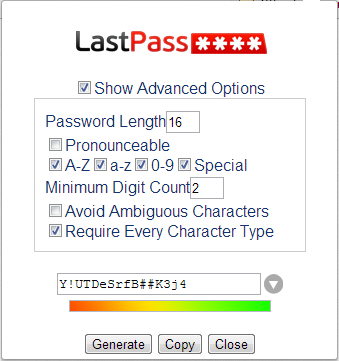
Products such as LastPass and KeePass are password managers that integrate with your browser. They can detect when you are logging in to a new site and offer to generate a password for you, or you can use them to generate a password for a site you already have a password for. They remember those passwords for you and keep them safe. KeePass is completely free, although takes a little more work if you use more than one computer. LastPass has a free option and works very well across multiple computers. There aren't a ton of reasons to purchase the very inexpensive subscription to LastPass, but one reason is that you can enable two-factor authentication on it, making your passwords even more secure. This is slightly more advanced, and not strictly necessary. Just using one of these products or another like them in your daily browsing will immensely increase your security online.
Once you have one of these products installed, make sure it's generating sufficiently secure passwords for you. I use LastPass, and the first time I'm generating a password I show the advanced options, set the length to 16 characters, make sure that A-Z, a-z, and 0-9 are all checked, that there is a minimum digit count and that every character type is required. Checking "Special Characters" will make your passwords even stronger, but some sites do not support them.
Here are two videos on what LastPass is and getting started with it. There are many more here.
I advocate LastPass because it's what I use and I've found it to work very well for me. This is by no means the only product available, feel free to search for alternatives that you are more comfortable with.
Final tips: Let's take a moment to think about security outside of browsing from home. When you are using a computer that does not belong to you, sign out of any websites you sign in to, and close the browser completely when finished. If you receive an e-mail with an attachment, think before opening it. If the attachment is anything but an image or movie, I would be wary of opening it, and even media files can be unsafe. Find other ways of sharing media, such as imgur or flickr for pictures, and YouTube for videos. Send links to sites where you can download software rather than sending the software itself. At the end of the day, if you aren't 100% certain what you're about to click on is safe, start by asking whoever sent it to you if they actually did send it.